For Chief Information Security Officers
- Home
- GRC Solutions
- For Chief Information Security Officers
Security and Compliance. Finally in the Same Place.
You own controls. Compliance tracks them separately. That disconnect creates risk and audit pain.
The reality of security-compliance overlap
Security and compliance should reinforce each other. In most organizations, they run on parallel tracks. Different systems, different evidence, different reporting. The overlap creates duplication. The gaps create risk.
1
Duplicate evidence requests
Security audits ask for control evidence. Compliance audits ask for the same evidence in a different format. You produce it twice.
2
Compliance gaps you don't see
Compliance teams track regulatory obligations in their own systems. You find out about gaps when they become findings.
3
CERT-In reporting as a manual process
Incident reporting timelines are tight. Six hours for certain incidents. If your workflow isn't built for it, you're building it during the incident.
4
Security posture ≠ compliance posture
You know your controls are strong. But compliance teams track a different set of metrics. The board sees two different stories.
What changes with eQomply
eQomply connects security controls to compliance requirements. One evidence source. One reporting layer. No more parallel tracks.
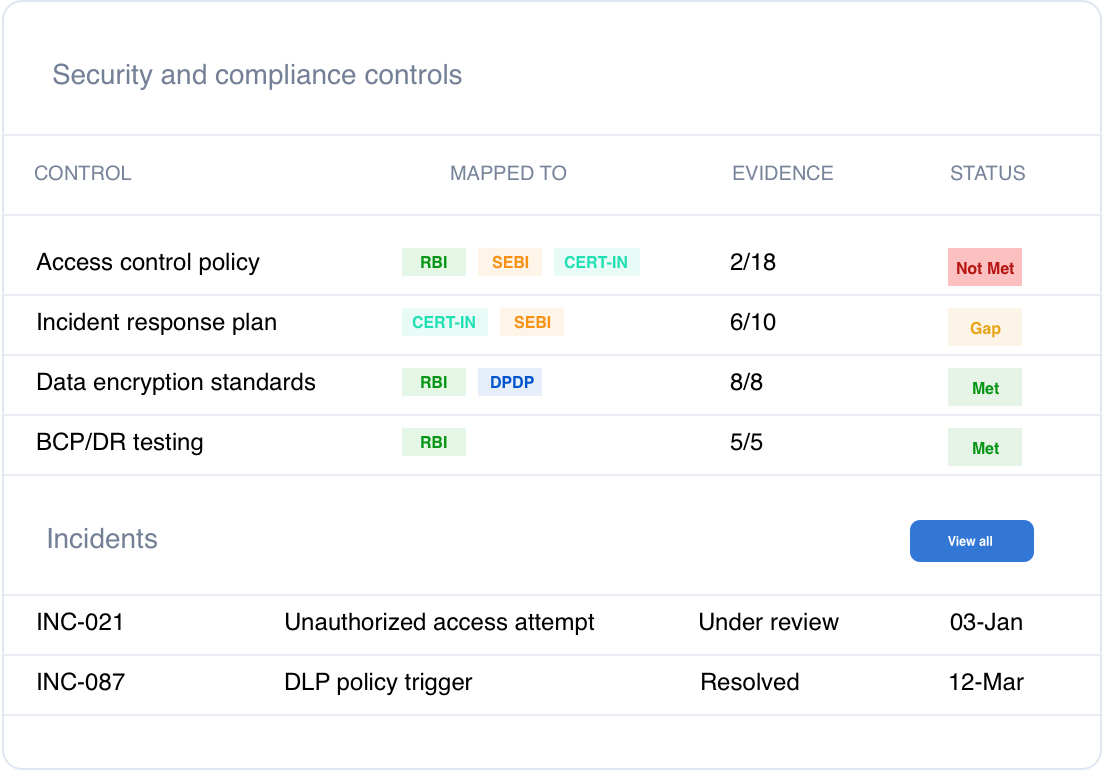
Unified control framework
Security controls and compliance requirements mapped together. Evidence captured once, used everywhere.
Visibility into compliance gaps
See which regulatory requirements overlap with your controls. Know where gaps exist before auditors find them.
CERT-In incident workflows
Incident classification, escalation, reporting. Built into the platform. Not built during the incident.
One version of the truth
Security and compliance report from the same data. The board sees one story, not two.
Evidence captured once, used everywhere
Control evidence logged at the source. Available for security audits, compliance reviews, and board reporting without duplicate requests.
Regulatory change tracking
New CERT-In directive or SEBI cybersecurity requirement lands. See how it maps to your existing controls. Identify gaps before they become findings.
Use Cases
See how this works in practice
RBI asks for evidence of access controls. Instead of producing it separately for the security team and the compliance team, you export once. Same evidence. Same source.
A reportable incident occurs. Classification triggers the right workflow. Escalation happens automatically. Reporting deadline tracked. Evidence preserved.
A new SEBI cybersecurity requirement lands. You see immediately which existing controls map to it and where gaps exist.
See how eQomply works for security and compliance alignment
A walkthrough tailored to your control environment.
